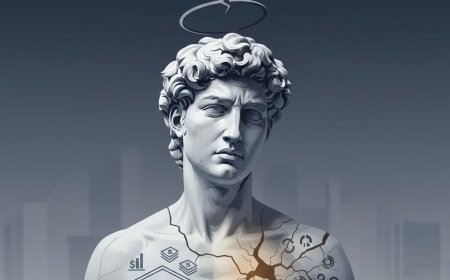
Audit Series: Compliance ≠ Security | Why Passing Audits Doesn’t Mean You Are Safe
A governance and cybersecurity analysis explaining why compliance does not equal security, and how organizations remain vulnerable despite passing audits, with insights on operational risk, frameworks, and real-world breaches.

Most leaders think doing what rules demand keeps them safe. Yet safety never shows up just because paperwork passes. A checkmark on a form only says someone followed steps yesterday. Real protection needs more than ticking boxes. Meeting standards feels right until trouble hits. Confidence built on audits fades fast when attacks come. Rules cover some risks, not all threats. What gets measured in reports often misses hidden gaps. Passing review gives peace of mind till it doesn’t. Being ready means going beyond what auditors ask.
It starts quietly such as paperwork looking flawless, like a company fresh off a clean SOC 2 report. Policies stand strong, controls line up neatly against standards, roles are spelled out without gaps, each box checked with proof attached, everything humming on paper. But then auditors look past files and into real operations. That is where things begin to fray. A flaw surfaces in how updates are handled across vital systems. Months pass without patches applied, even though fixes sit ready, leaving weaknesses wide open. Leadership brushes it off relying that compliance has been met, so the concern feels overstated. That response like calm, firm is wrong which shows how easily ticking boxes replaces guarding against harm.
MORE READ:
- Lagos International Financial Centre: Nigeria’s New Economic Blueprint
- How Corporate Governance Drives the Survival and Growth of Emerging Enterprises
- Why Strong Corporate Governance Is the Secret to African Business Survival
- Digital Governance in Nigeria, Why Corporate Boards Must Treat AI, Cybersecurity and Data Ethics as Fiduciary Duties
From there, the pattern becomes clearer.
Most rule sets are built by looking back. They grow out of past failures, recognized weak spots, and shared lessons. But staying secure does not look backward. It moves ahead. It shifts constantly. It responds to attackers who never stop evolving. What gets checked in audits rarely reflects what happens when systems face live threats. Meeting checklist demands does not mean defenses will hold under pressure. Many organizations follow rules perfectly yet still break when tested differently.
This is no longer abstract. It has played out repeatedly at scale. The breach at Equifax remains one of the clearest examples. Controls existed. Standards were met. Yet a known vulnerability remained unpatched for months, and attackers exploited it. The failure was not in design. It was in execution. That distinction matters.

It leads directly to a deeper issue—what I call the comfort of compliance.
Most of this gap comes down to habit. Compliance turns into paperwork drills—tracking, filing, gathering proofs, clearing audits. Once that is done, follow-through fades. Controls remain on paper, not in practice. Ownership becomes blurred. Monitoring runs, yet alerts go unanswered. Security looks solid until it is tested. Real attacks ignore documents. They hunt live flaws, everywhere, nonstop, piling up chances until something breaks.
And the odds are not balanced.
Audits move step by step, checking pieces at set intervals. Attackers move without limits. They scan entire environments, not samples. They act in real time, not quarterly cycles. A gap ignored for seconds becomes a door left open. Systems pass checks and still collapse—not because rules are broken, but because they are misunderstood. Checklists were treated as finish lines instead of starting points.
To make this distinction clearer, the contrast must be stated plainly:
This is where many organizations need to reset their thinking.
Compliance is not the destination. It is groundwork. It brings order. It defines roles. It creates consistency. Frameworks such as ISO 27001, SOC 2, and the NIST Cybersecurity Framework provide structure that organizations need. But structure alone does not defend anything. It only prepares the ground. Security is what is built on top of that ground. And that requires motion.
It requires continuous vulnerability management, real-time monitoring, threat intelligence, and deliberate testing—penetration testing, red teaming, and scenario simulations that reflect how attacks actually happen. Without these, compliance remains static while risk remains active.
This shift is also changing what auditing itself must become.
Auditing can no longer stop at confirming that controls exist. It must go further—testing whether those controls work when conditions are no longer ideal. That means asking harder questions, not just more questions. Not “is there a policy,” but “does it hold under pressure?” Not “is there evidence,” but “what happens when this fails?” That transition from validation to interrogation is where real value now sits.
Because in practice, the gap between written intent and operational reality is where risk accumulates. Access reviews are defined but delayed. Incident response plans exist but remain untested. Patch cycles are documented but deferred under operational pressure. These are not compliance failures on paper. They are security failures in reality.
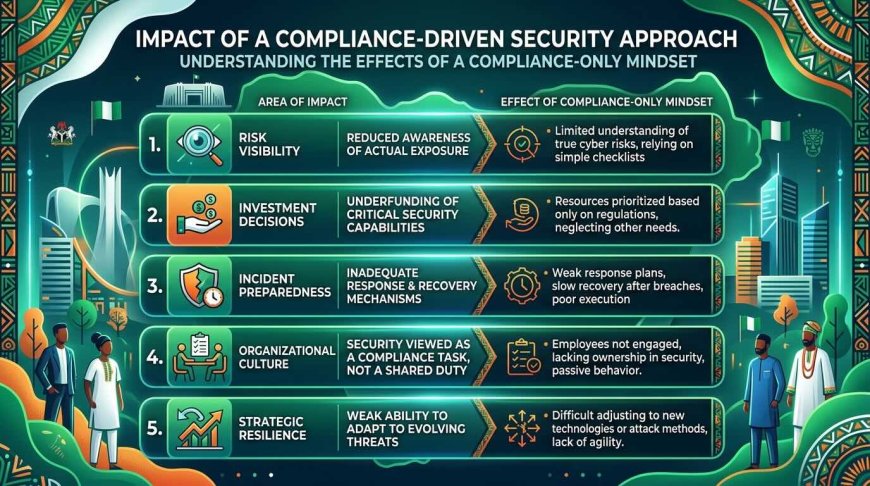
And they are costly. The cost of this misplaced confidence shows up across the organization:

Over time, something subtle but dangerous happens. Confidence grows. Visibility shrinks. Risk becomes invisible—not because it is absent, but because it is misunderstood. That is where leadership must become deliberate.
Security does not improve through policy alone. It improves through habit. Through repetition. Through ownership. Through systems that are watched continuously, not reviewed occasionally. Through teams that know what they are responsible for—and are measured by how well controls perform, not how well they are documented. It becomes part of how the organization operates. Not something it prepares for once a year.
At that point, the question facing leadership becomes unavoidable: are we building systems to pass audits, or systems to withstand attacks? Because both require investment—but only one builds resilience. Audit success may satisfy regulators. It may reassure stakeholders. But it does not stop an attacker. Resilience does. Resilient organizations see what is happening across their systems in real time. They respond quickly. They design for failure, not just success. They build redundancy. They test their assumptions. And most importantly, they learn—continuously, deliberately, and without waiting for an audit to expose what is already broken.
That is the difference between appearing secure and actually being secure. In the end, the lesson is simple, but it is often ignored:
- Documentation is not defense.
- Frameworks are not protection.
- Passing an audit is not security.
Compliance gives structure. It assigns responsibility. It creates a baseline. But security lives elsewhere.
It lives in execution. In discipline. In the quiet, consistent work done when no one is watching. It lives in questioning what passed yesterday and testing what might fail tomorrow. It lives in closing gaps before they are exploited—not after they are reported. Because attackers are not reading your policies. They are testing your systems. And safety, no matter how well documented, is never stored in binders.
About the Author:
Dr Ohio O. Ojeagbase is a multidisciplinary governance, risk, and corporate strategy expert whose practice spans non-performing loan securitisation, debt re-engineering, debt factoring, and corporate debt restructuring, alongside advanced private investigation capabilities and enterprise risk intelligence. His expertise integrates financial recovery architecture with investigative precision, enabling organizations to address distressed assets, trace exposure pathways, and redesign debt structures in ways that restore liquidity while preserving long-term value. Within the GRC and AI governance landscape, he operates at the intersection of compliance assurance, operational risk, and digital-era control frameworks, helping organizations align regulatory obligations with emerging risks in data, automation, and cybersecurity systems. His private investigation capability further strengthens this position by providing forensic-level insight into asset integrity, transactional anomalies, and hidden operational vulnerabilities that standard audit mechanisms often overlook. Collectively, his work supports institutions in embedding security of assets, governance discipline, and financial sustainability at the core of enterprise strategy, ensuring that organizations not only comply with regulatory expectations but also build resilient systems capable of sustaining value across generations.
Contact: report@probitasreport.com
Stay informed and ahead of the curve! Follow The Probitas Report on WhatsApp for real-time updates, breaking news, and exclusive content especially on integrity in business and financial fraud reporting. Don’t miss any headlines, connect with us on social media @probitasreport and visit www.probitasreport.com WhatsApp Only: +234 902 148 8737
[©2026 ProbitasReport - All Rights Reserved. Reproduction or redistribution requires explicit permission.]
What's Your Reaction?